“Working with Roeing has been a great experience. They really care about delivering the product that was requested. We’ve found them to be accessible, responsive, and creative. We wouldn’t hesitate to work with them again on another project, or recommend them to others.”
– Eric Grossman, Tippecanoe County Assessor
Security Services 
When it comes to security, our job as your technology partner is to reduce your risk by delivering solutions that are designed to detect and stop a security breach. We take very seriously our responsibility to assist you in protecting the continuity of your business.
New vulnerabilities and exploits are discovered on a daily basis and with threats as prevalent and damaging as Ransomware, data theft, and system breaches, it is critical to quickly identify and mitigate vulnerabilities. An effective security strategy is a layered defense approach, built on leading security technologies that address the wide spectrum of threats and compliance requirements.
Roeing’s Secure360 suite provides a layered approach to protecting your business with an integrated solution stack of security products that are built on the NIST (National Institute of Standards and Technology) Cybersecurity Framework: Identify, Protect, Detect, Respond and Recover.
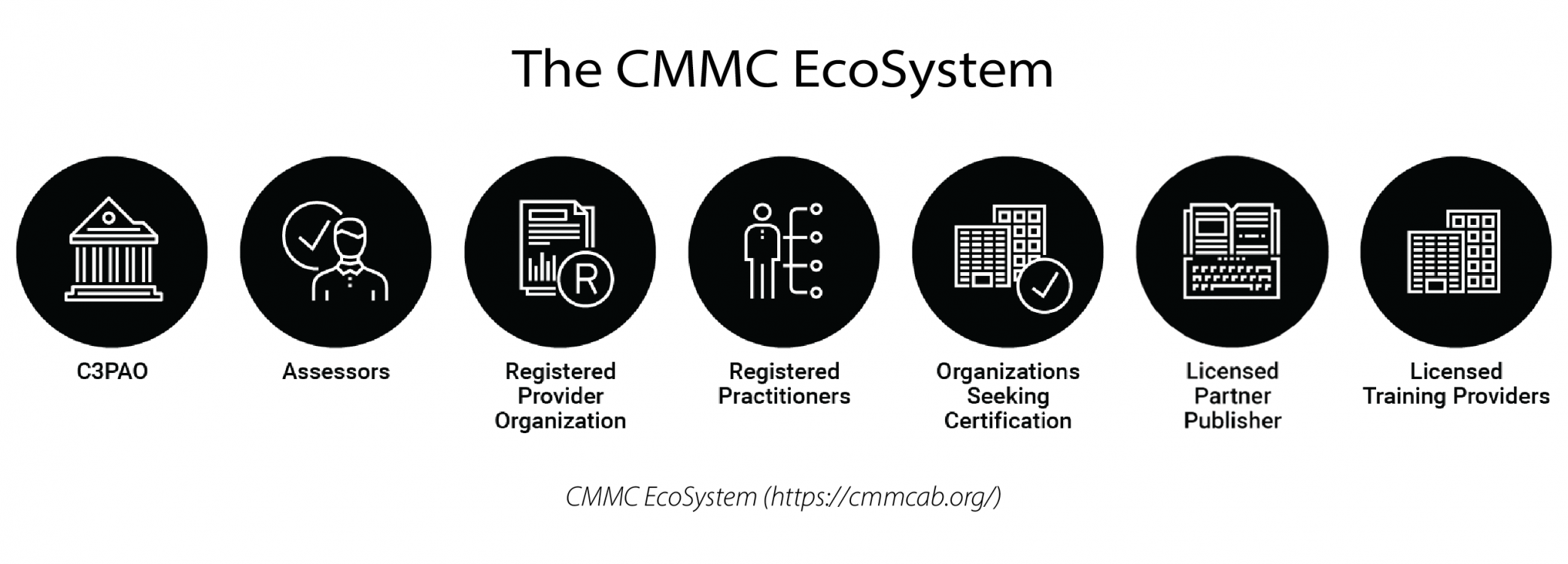
Through the Cybersecurity Maturity Model Certification (CMMC) Accreditation Body (AB), Cyle Dibble, Director of Client Engagement, has been certified as a CMMC Registered Practitioner. This enables Roeing to provide Pre-Assessment Readiness Reviews (PARR).
The Roeing Secure360 product suite aligns the best practices of the NIST framework with a cost-effective solution to help you manage Cybersecurity-related risk.
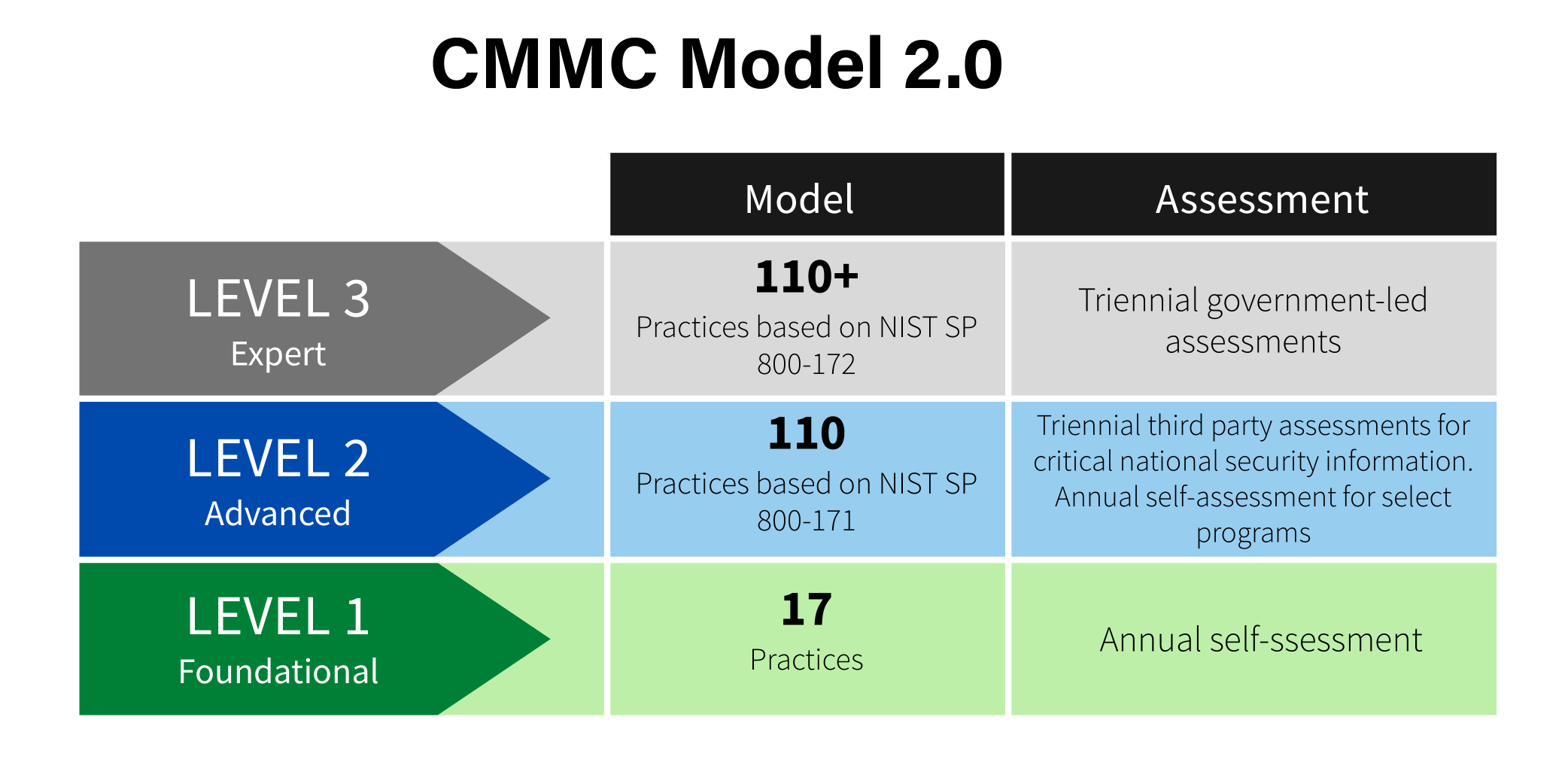
With Roeing's Director of Client Engagement certified as a Registered Practitioner through the CMMC Accreditation Body, Roeing has the ability to perform Pre-Assessment Readiness Reviews or PARRs. This provides a Pre-Assessment of your current progress towards meeting CMMC requirements.
Registered Practitioners (RP) provide advice, consulting, and recommendations in regards to your organizations readiness to successfully achieve CMMC accreditation. They are implementers and consultants but do not conduct Certified CMMC Assessments. They are not authorized to certify any assessment but exist to facilitate your CMMC journey.
Roeing does not conduct the final Certified Assessments.
Depending on your current cybersecurity maturity, as well as the CMMC level you are striving to achieve , the implementation of the needed documentation, procedures and suitable controls may take several months. Part of the CMMC Assessment is that you must show that your cybersecurity maturity is an integrated part of your organization for a substantial amount of time. By starting now to look at your current status and what changes you may or may not need to make, your organization will be saving valuable time and money, putting you well ahead of the curve and the competition.
Get help achieving compliance quickly and be ready for your Certified CMMC Assessment. Roeing is your partner to provide a clear implementation pathway to CMMC accreditation. Our PARR (Pre-Assessment Readiness Review) helps you build the needed documentation, make recommendations, and provide assistance in implementing the needed controls to achieve your appropriate CMMC Level.
Our Secure360 DETECT Security Assessment can be either a one-time snapshot in time of your environment or an ongoing Security Service with Quarterly Re-Checks that give you an accurate, in-depth view of how your Security footprint has improved.
Couple this with our Secure360 CVA (Continuous Vulnerability Assessment) Security Service and your Technology Infrastructure is covered from top-to-bottom.
With our Secure360 DETECT Assessments you receive in-depth reports that give you both the deep-dive technical information that you need to remediate and also the high-level, non-technical, executive view. Your environment will be assigned a Risk Analysis Score that identifies how your current environment is hardened against security threats. Any future assessments will utilize the Risk Analysis Score as a baseline to provide a comparison identifying the areas that have improved and where vulnerabilities still exist.
As network security threats grow more advanced by the day, protecting your company’s systems and data becomes more challenging. Knowing where your risks and vulnerabilities are is the first step to hardening up your network security.
Our Roeing Secure360 CVA (Continuous Vulnerability Assessment) solution takes into account your custom security policies and intelligently identifies suspicious anomalies, changes, and threats. In addition, our powerful analysis engine examines multiple data points and notifies you directly of security issues caused by unusual user behavior and network misconfigurations.
Roeing will set up regular reporting that details changes in your network from report to report, as well as all the issues we have resolved in that time. In addition, we take measures to minimize internal network vulnerabilities. These measures include setting up daily and weekly alerts, and delivering actionable intelligence—in case of an accidental or malicious breach.
The two biggest mistakes a company can make with respect to security is assuming their employees know internal security policies and care enough to follow those policies. There are many security risks that lead to data breaches but the most effective method is a phishing scam. The best defense against a Phishing Scam is user education and training your employees to be constantly wary of emails they receive.
The Roeing Secure360 Cybersecurity Education incorporates online user training with simulating Phishing emails to build awareness. Employees who click on the Phishing email links receive a message that they have fallen for a Phishing Scam and are offered tips or training on how to avoid being victimized in the future. Roeing Secure360 Cybersecurity Training educates the users about your plan and policies as well as build awareness of the common methods used to compromise a user’s credentials. This will help you create a “culture of security” where security is top of mind when accessing emails or using the internet.
Managed Security Threat Monitoring as-a-service.
One service includes all:
- 24/7 Security Operations Center (SOC)-as-a-service
- Cloud-based Security Information & Event Management (SIEM)-as-a-service
- Incident Response Team (IRT) and Forensics, IRT-as-a-service
- Monitor threats on-premise, Cloud (e.g., AWS, Azure) or hybrid
- One month opt-out. No penalty!
- One low monthly subscription fee per device
- One hour to implement Security Monitoring Solution
- Office365 Security Monitoring
- Over 250 products supported (e.g., Firewall, Domain controllers)
- Agentless cloud-based SIEM solution